LLNL researchers have developed a fabrication process for creating 3D random interdigitated architectures of anodes and cathodes, eliminating the need for a membrane to separate them. This approach is similar to the repeating interdigitated multi-electrode architectures that also were developed at LLNL.
Keywords
- Show all (50)
- Electric Grid (8)
- Carbon Utilization (6)
- Data Science (5)
- Materials for Energy Products (4)
- Additive Manufacturing (2)
- Computing (2)
- Direct Air Capture (2)
- Imaging Systems (2)
- Power Electronics (2)
- Simulation (2)
- Synthesis and Processing (2)
- Analysis (1)
- Geologic Storage (1)
- Inertial Fusion Energy (IFE) (1)
- Information Technology (1)
- Membranes (1)
- Quantum Science (1)
- Spectrometers (1)
- (-) Cybersecurity (4)
- (-) 3D Printing (2)
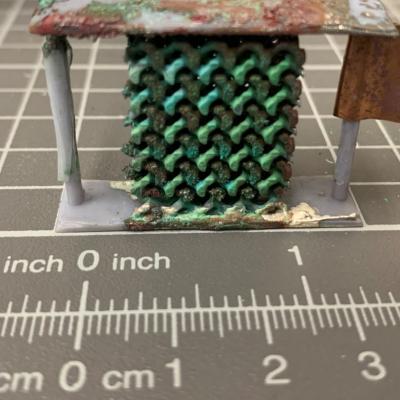
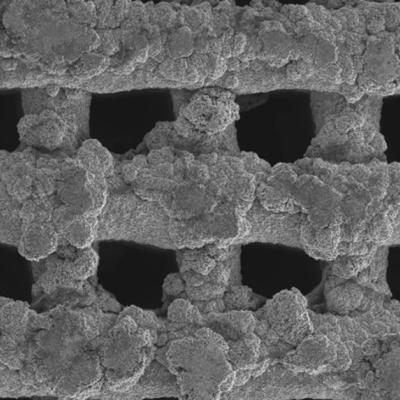
Improving the active material of the Zn anode is critical to improving the practicality of Zn-MnO2 battery technology. LLNL researchers have developed a new category of 3D structured Zn anode using a direct-ink writing (DIW) printing process to create innovative hierarchical architectures. The DIW ink, which is a gel-based mixture composed of zinc metal powder and organic binders, is extruded…
CSP-POST provides the capability to inspect all incoming and outgoing emails while providing after-the-fact forensic capabilities. Using commercially available lightweight and serverless technologies, CSP-POST easily collects all email and parses it into easily searchable metadata, enriched and ready for analysis. The web-based application is deployed in a repeatable, testable, and auditable…
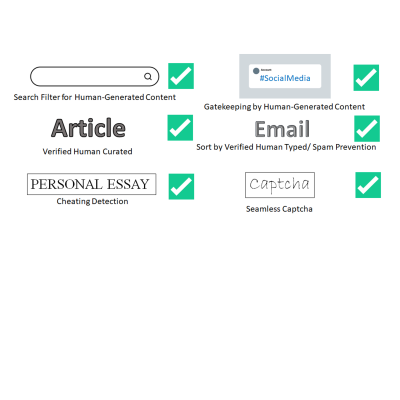
LLNL has invented a new system that uses public key cryptography to differentiate between human-generated text and AI-generated text. This invention can be used to validate that text is likely to be human generated for the purposes of sorting or gatekeeping on the internet, can detect cheating on essay assignments, and can be used as an automatic captcha that does away with the hassle of…

LLNL has developed a new method for securely processing protected data on HPC systems with minimal impact on the existing HPC operations and execution environment. It can be used with no alterations to traditional HPC operations and can be managed locally. It is fully compatible with traditional (unencrypted) processing and can run other jobs, unencrypted or not, on the cluster simultaneously…
LLNL's NeMS system enables network mapping operations by using two LLNL-developed software systems: LLNL's NeMS tool and the Everest visualization system. Each software system can be also used separately for their specific applications. When the two systems are used together as an iterative analysis platform, LLNL's NeMS system provides network security managers and information technology…
