CSP-POST provides the capability to inspect all incoming and outgoing emails while providing after-the-fact forensic capabilities. Using commercially available lightweight and serverless technologies, CSP-POST easily collects all email and parses it into easily searchable metadata, enriched and ready for analysis. The web-based application is deployed in a repeatable, testable, and auditable…
Keywords
- Show all (207)
- Instrumentation (39)
- Additive Manufacturing (37)
- Sensors (16)
- Synthesis and Processing (16)
- Diagnostics (13)
- Photoconductive Semiconductor Switches (PCSS) (9)
- Electric Grid (8)
- Imaging Systems (8)
- 3D Printing (7)
- Materials for Energy Products (7)
- Carbon Utilization (6)
- Semiconductors (6)
- Compact Space Telescopes (5)
- Data Science (5)
- Therapeutics (5)
- Diode Lasers (4)
- Laser Materials Processing (4)
- Material Design (4)
- Optical Switches (4)
- (-) Cybersecurity (4)
Technology Portfolios
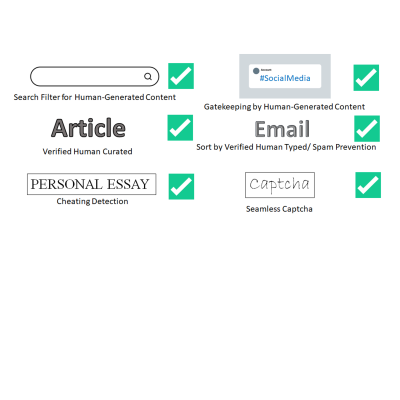
LLNL has invented a new system that uses public key cryptography to differentiate between human-generated text and AI-generated text. This invention can be used to validate that text is likely to be human generated for the purposes of sorting or gatekeeping on the internet, can detect cheating on essay assignments, and can be used as an automatic captcha that does away with the hassle of…
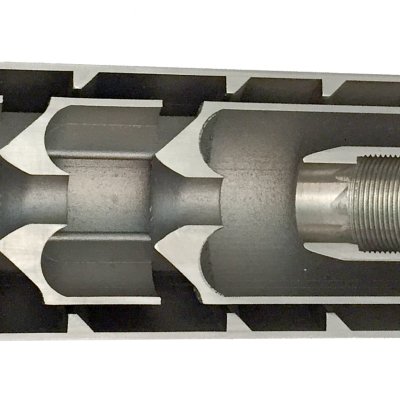
The suppressor has a series of chambers for the propellant to flow through, but unlike all traditional suppressors, the chambers are open, not closed. The propellant is not trapped. It keeps moving. We manage its unimpeded flow through the suppressor. This is the key underlying technology of our suppressor design that enables all the improvements over the 100-year old traditional designs.

Livermore Lab researchers have developed a tunable shaped charge which comprises a cylindrical liner commonly a metal such as copper or molybdenum but almost any solid material can be used and a surround layer of explosive in which the detonation front is constrained to propagate at an angle with respect to the charge axis. The key to the concept is the ability to deposit a surrounding…
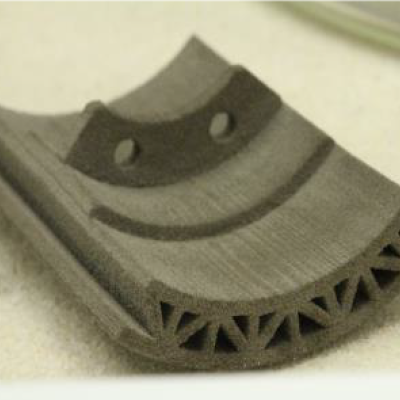
Livermore Lab researchers have developed a method that combines additive manufacturing (AM) with an infill step to render a final component which is energetic. In this case, AM is first used to print a part of the system, and this material can either be inert or energetic on its own. A second material is subsequently added to the structure via a second technique such as casting, melt…

LLNL has developed a new method for securely processing protected data on HPC systems with minimal impact on the existing HPC operations and execution environment. It can be used with no alterations to traditional HPC operations and can be managed locally. It is fully compatible with traditional (unencrypted) processing and can run other jobs, unencrypted or not, on the cluster simultaneously…
LLNL's NeMS system enables network mapping operations by using two LLNL-developed software systems: LLNL's NeMS tool and the Everest visualization system. Each software system can be also used separately for their specific applications. When the two systems are used together as an iterative analysis platform, LLNL's NeMS system provides network security managers and information technology…