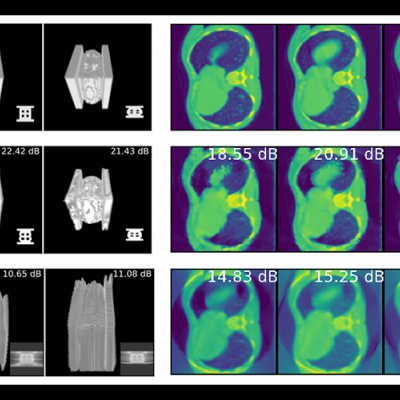
LLNL’s Distributed Implicit Neural Representation (DINR) is a novel approach to 4D time-space reconstruction of dynamic objects. DINR is the first technology to enable 4D imaging of dynamic objects at sufficiently high spatial and temporal resolutions that are necessary for real world medical and industrial applications.

The essence of this invention is a method that couples network architecture using neural implicit representations coupled with a novel parametric motion field to perform limited angle 4D-CT reconstruction of deforming scenes.
CSP-POST provides the capability to inspect all incoming and outgoing emails while providing after-the-fact forensic capabilities. Using commercially available lightweight and serverless technologies, CSP-POST easily collects all email and parses it into easily searchable metadata, enriched and ready for analysis. The web-based application is deployed in a repeatable, testable, and auditable…
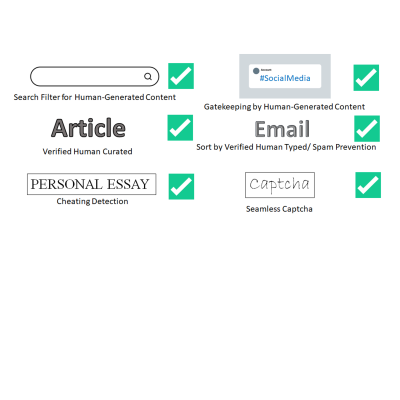
LLNL has invented a new system that uses public key cryptography to differentiate between human-generated text and AI-generated text. This invention can be used to validate that text is likely to be human generated for the purposes of sorting or gatekeeping on the internet, can detect cheating on essay assignments, and can be used as an automatic captcha that does away with the hassle of…
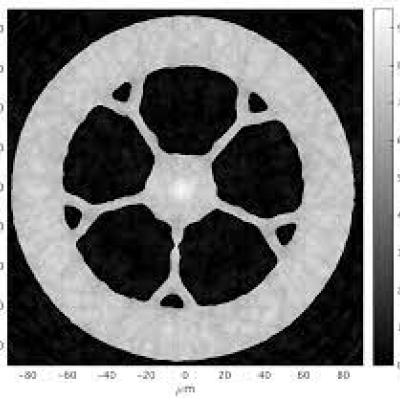
To solve these challenges using new and existing CT system designs, LLNL has developed an innovative software package for CT data processing and reconstruction. Livermore Tomography Tools (LTT) is a modern integrated software package that includes all aspects of CT modeling, simulation, reconstruction, and analysis algorithms based on the latest research in the field. LTT contains the most…

LLNL has developed a new method for securely processing protected data on HPC systems with minimal impact on the existing HPC operations and execution environment. It can be used with no alterations to traditional HPC operations and can be managed locally. It is fully compatible with traditional (unencrypted) processing and can run other jobs, unencrypted or not, on the cluster simultaneously…