CSP-POST provides the capability to inspect all incoming and outgoing emails while providing after-the-fact forensic capabilities. Using commercially available lightweight and serverless technologies, CSP-POST easily collects all email and parses it into easily searchable metadata, enriched and ready for analysis. The web-based application is deployed in a repeatable, testable, and auditable…
Keywords
- (-) Show all (240)
- Additive Manufacturing (55)
- Instrumentation (41)
- Synthesis and Processing (21)
- Sensors (14)
- Diagnostics (11)
- Imaging Systems (9)
- Photoconductive Semiconductor Switches (PCSS) (9)
- 3D Printing (8)
- Carbon Utilization (7)
- Electric Grid (7)
- Materials for Energy Products (7)
- Semiconductors (7)
- Substrate Engraved Meta-Surface (SEMS) (7)
- Therapeutics (7)
- Compact Space Telescopes (6)
- Brain Computer Interface (BCI) (5)
- Data Science (5)
- Diode Lasers (5)
- Optical Switches (5)
- Laser Materials Processing (4)
Technology Portfolios
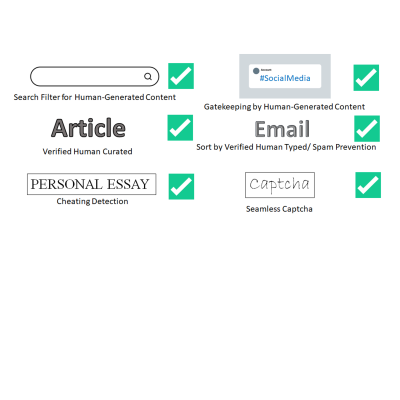
LLNL has invented a new system that uses public key cryptography to differentiate between human-generated text and AI-generated text. This invention can be used to validate that text is likely to be human generated for the purposes of sorting or gatekeeping on the internet, can detect cheating on essay assignments, and can be used as an automatic captcha that does away with the hassle of…
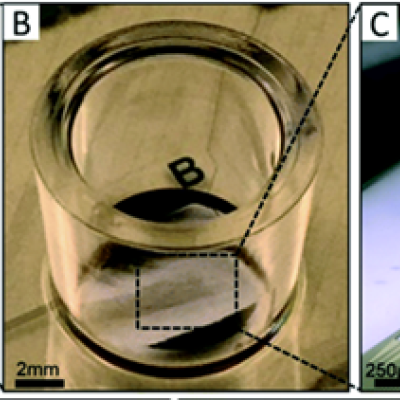
To replicate the physiology and functionality of tissues and organs, LLNL has developed an in vitro device that contains 3D MEAs made from flexible polymeric probes with multiple electrodes along the body of each probe. At the end of each probe body is a specially designed hinge that allows the probe to transition from lying flat to a more upright position when actuated and then…

LLNL has developed a new method for securely processing protected data on HPC systems with minimal impact on the existing HPC operations and execution environment. It can be used with no alterations to traditional HPC operations and can be managed locally. It is fully compatible with traditional (unencrypted) processing and can run other jobs, unencrypted or not, on the cluster simultaneously…