LLNL researchers have developed a method to of crosslinking, polymerizing or otherwise covalently coupling a subset of nitroaromatic and nitramine explosive molecules and compositions. Energetic materials manufactured using the novel method can be used ‘neat’ or as an energetic binder phase for another unmodified energetic compound. The approach may also be employed to co-…
Keywords
- (-) Show all (240)
- Additive Manufacturing (55)
- Instrumentation (41)
- Synthesis and Processing (21)
- Sensors (14)
- Diagnostics (11)
- Imaging Systems (9)
- Photoconductive Semiconductor Switches (PCSS) (9)
- 3D Printing (8)
- Carbon Utilization (7)
- Electric Grid (7)
- Materials for Energy Products (7)
- Semiconductors (7)
- Substrate Engraved Meta-Surface (SEMS) (7)
- Therapeutics (7)
- Compact Space Telescopes (6)
- Brain Computer Interface (BCI) (5)
- Data Science (5)
- Diode Lasers (5)
- Optical Switches (5)
- Laser Materials Processing (4)
Technology Portfolios

LLNL has developed a method that adds a polyamine based crosslinker and an acid receptor, based on MgO nanoparticles into a polymer bonded PBX, where the polymer binder is a fluoropolymer containing vinylidene difluoride functionality. Crosslinking kinetics can then be controlled by selecting an appropriate amine structure, pressing temperature and optionally the addition of a chemical…

LLNL researchers uses Additive Manufacturing (AM) to create reinforcing scaffolds that can be integrated with High Explosives (HE) or solid rocket fuel with minimal volume fraction. Its main benefit is to create stability in harsh field conditions. Its secondary benefit is providing another method to finely tune blast performance or fuel burn. Creating complex shapes with structural…
CSP-POST provides the capability to inspect all incoming and outgoing emails while providing after-the-fact forensic capabilities. Using commercially available lightweight and serverless technologies, CSP-POST easily collects all email and parses it into easily searchable metadata, enriched and ready for analysis. The web-based application is deployed in a repeatable, testable, and auditable…
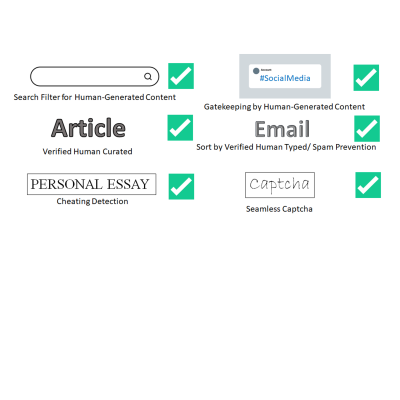
LLNL has invented a new system that uses public key cryptography to differentiate between human-generated text and AI-generated text. This invention can be used to validate that text is likely to be human generated for the purposes of sorting or gatekeeping on the internet, can detect cheating on essay assignments, and can be used as an automatic captcha that does away with the hassle of…

LLNL has developed a new method for securely processing protected data on HPC systems with minimal impact on the existing HPC operations and execution environment. It can be used with no alterations to traditional HPC operations and can be managed locally. It is fully compatible with traditional (unencrypted) processing and can run other jobs, unencrypted or not, on the cluster simultaneously…

